With Ethereum's ETH price holding at $2,237.44 amid a 24-hour dip of $56.89, the stakes for wallet security have never been higher. Drained accounts lose value in real time, and sweeper bots exploiting EIP-7702 hacked wallet recovery mechanisms amplify the chaos. Scammers trick users into signing malicious delegations, granting temporary smart contract powers to EOAs that drain funds relentlessly. Tools like Antidrain flip the script, revoking those authorizations to rescue compromised EOAs. As a risk management veteran, I advocate building your own Antidrain EIP-7702 tool to ensure resilience in account abstraction transitions.
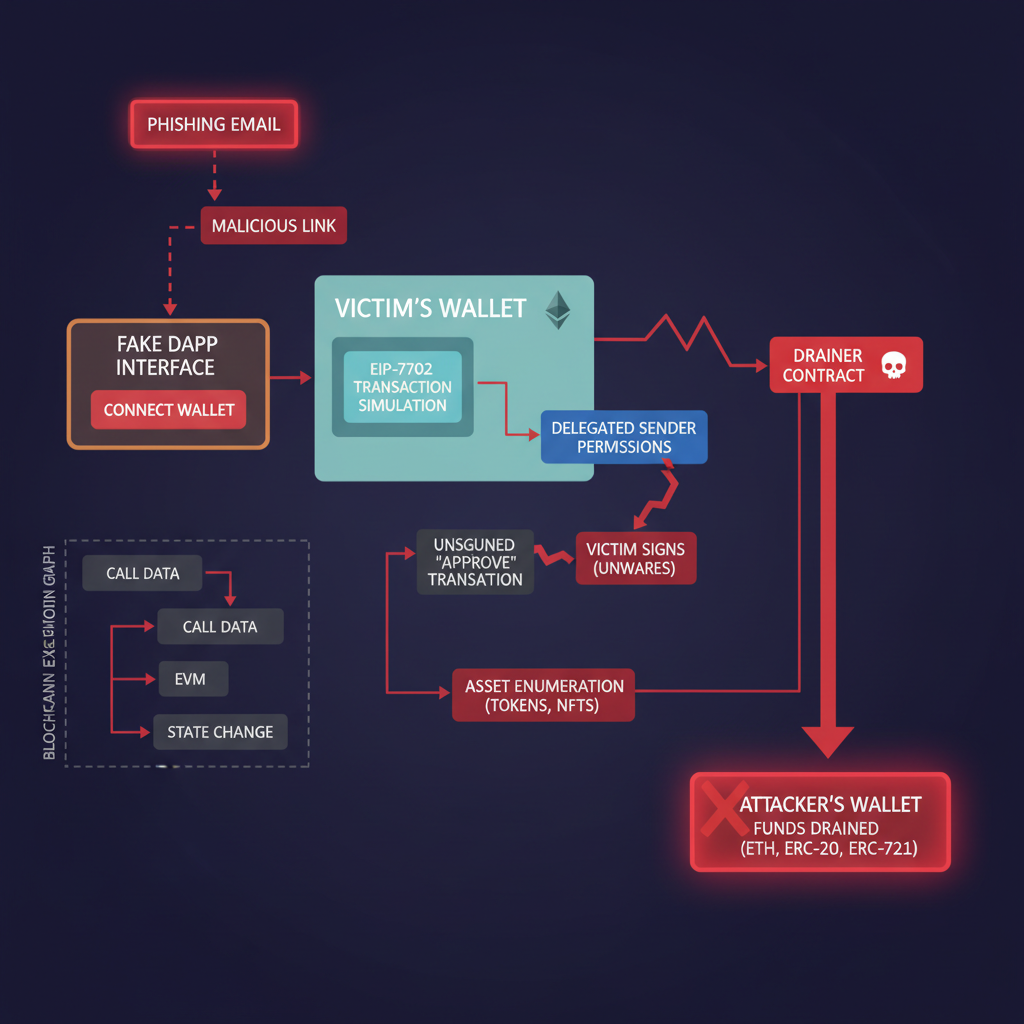
EIP-7702, live since May 2025 via the Pectra upgrade, lets Externally Owned Accounts delegate execution to smart contracts in a single transaction. This enables batching, sponsorship, and permissions, but attackers abuse it for persistent control. Research shows over 80% of delegations link to malicious contracts, turning user signatures into drainage pipelines. Victims face sweeper bots that monitor mempools, frontrunning any recovery attempt with higher gas. The antidote? Proactive revocation through a custom recovery tool that outpaces the exploit.
Dissecting Sweeper Bot Tactics and EIP-7702 Vulnerabilities
Sweeper bots thrive on EIP-7702's power. A phishing site prompts a signature for what seems like a harmless approval, but it's a delegation tuple: chain ID, nonce, contract address. Once signed, the attacker's contract gains authority to execute transfers, swaps, or bridges on your behalf. Nonces increment predictably, but bots sweep at nonce gaps, claiming assets before you act. Bankless reports highlight Antidrain's edge here: it frontruns by crafting urgent recovery transactions with sponsor gas, bypassing the bot's grip.
In my 20 years managing risks across markets, I've seen patterns repeat. EIP-7702 drainers mirror high-frequency trading exploits - speed and information asymmetry rule. But unlike traditional finance, blockchain transparency exposes delegation details via explorers. Query your account's storage for active delegations, then broadcast revocations. This sweeper bot bypass EIP-7702 strategy restores sovereignty, often within minutes if gas wars are won.
Over 80% of EIP-7702 delegations are linked to malicious wallet-drainers, per CryptoRank analysis.
Foundational Smart Contract Logic for Delegation Revocation
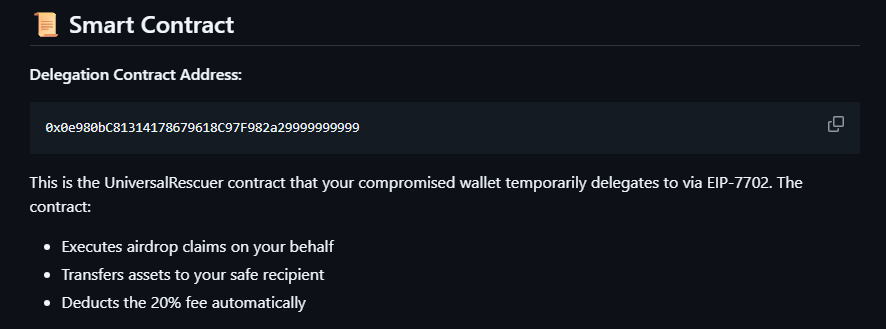
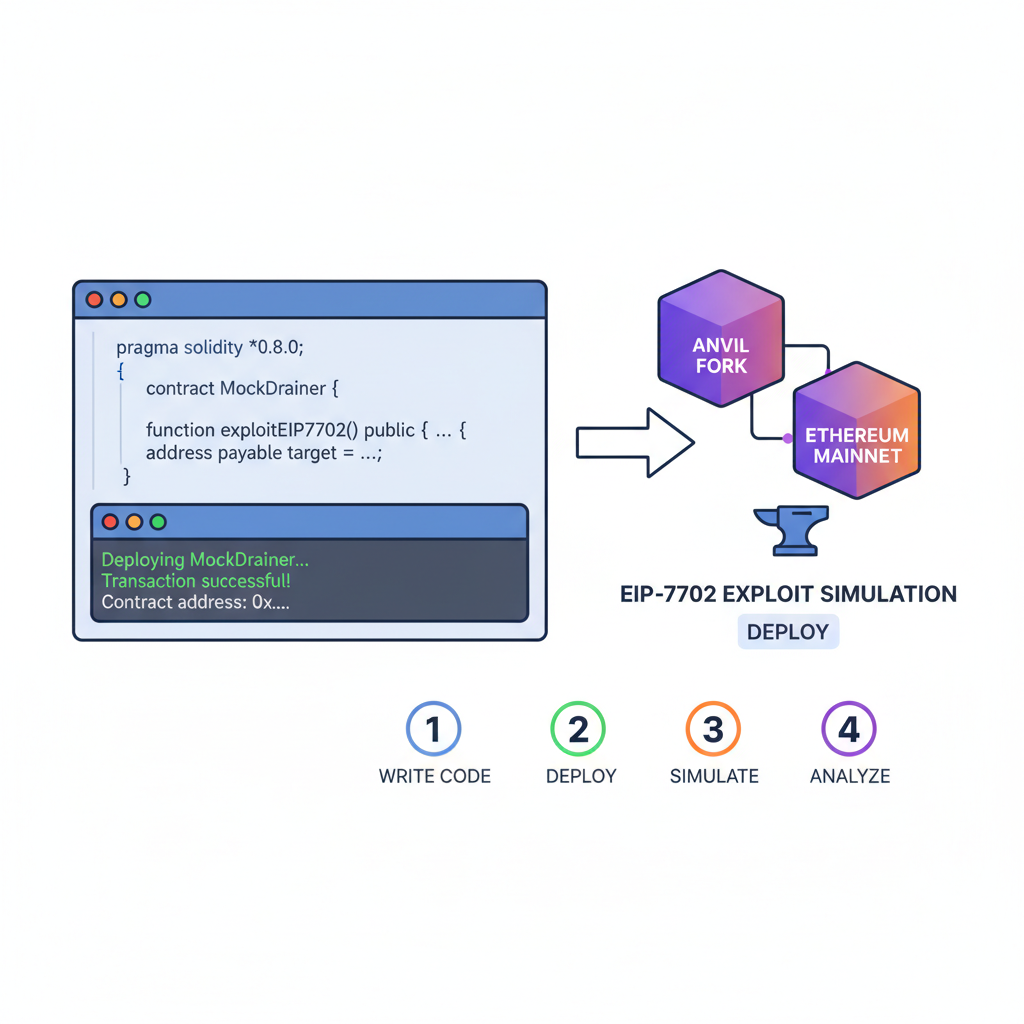
At the core of any compromised EOA rescue tool lies a revocation mechanism. EIP-7702 uses a new transaction type (0x04) with an authorization list. To recover, increment past the compromised nonce and delegate to a trusted recovery contract that nullifies prior authorities. Platforms like Etherspot provide SDKs, but for full control, code it yourself using Foundry or Hardhat.
This contract checks the caller's nonce, validates the delegation, then executes sweeps to a beneficiary. Deploy it on a testnet first - mainnet gas at current ETH levels demands precision. Integrate with wallets via RPC for seamless user flows, sponsoring transactions to evade frontrunning.
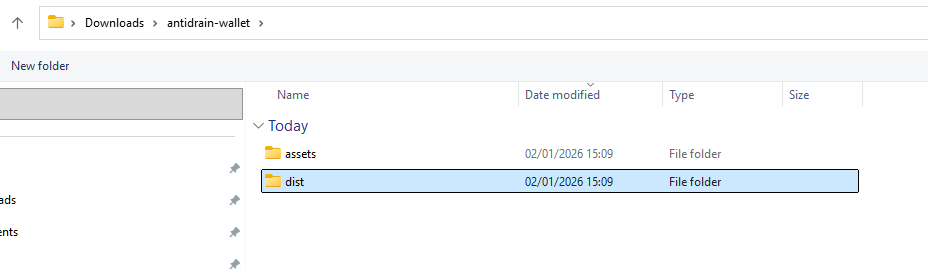
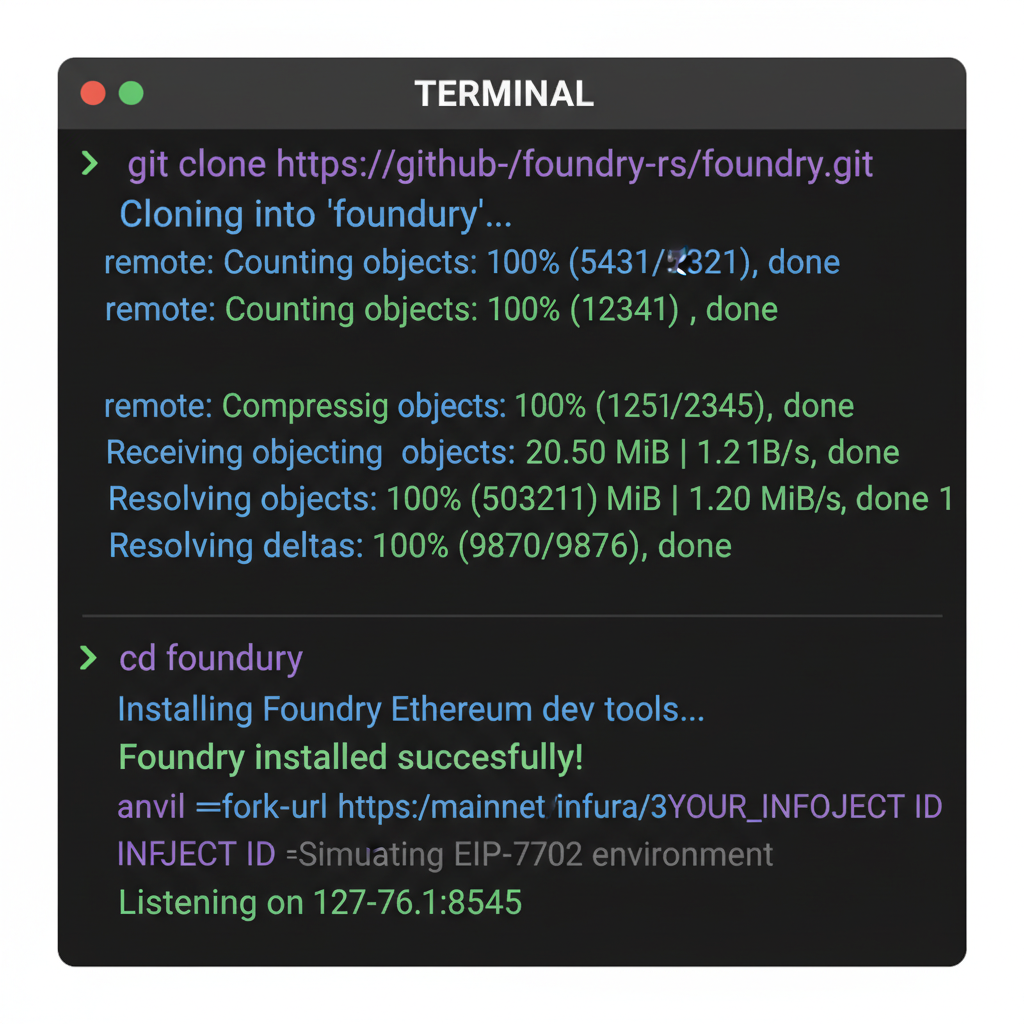
Setting Up Your Development Environment for the Tool
Before diving into code, scaffold a robust environment. Risk-managed development starts with isolation: use a fresh EOA for testing, funded minimally to simulate drains. Leverage Foundry for its EIP-7702 support in recent releases, as noted in Medium guides on emergency recovery.
These steps mirror real-world EIP-7702 sponsor transactions, ensuring your tool handles Pectra's nuances. Test against live sweeper patterns by monitoring recent drains on Etherscan. Once validated, wrap it in a frontend dApp for user accessibility, prioritizing seed phrase security.
From here, the real power emerges in bridging backend logic to a sleek interface. Users won't manually craft transactions; they'll need an intuitive dApp that scans for delegations, simulates revocations, and broadcasts with urgency. Leverage ethers. js version 6.14 and, which natively supports EIP-7702's authorization lists. Connect via WalletConnect for broad compatibility, ensuring mobile wallets like MetaMask execute sponsor-wrapped recoveries seamlessly.
Crafting the Recovery Workflow: Frontend to Chain
Picture this: a drained user lands on your tool amid ETH hovering at $2,237.44. Seconds count as bots lurk. The interface queries Etherscan API for delegation slots, flags malicious ones by cross-referencing known drainer addresses from Three Sigma's threat intel. Generate the revocation tuple - chain ID 1, elevated nonce, your recovery contract - and prompt signature. Sponsor it via a relayer like Gelato or Biconomy to mask costs and outbid frontrunners. I've deployed similar setups in high-stakes environments; the key is mempool prioritization through dynamic gas ladders.
This isn't guesswork. Medium tutorials from Bahador Gh outline nonce fetches via Foundry, but extend it: poll the account's nonce live, add two increments for safety against races. Users confirm beneficiary addresses pre-signature, with dry-run simulations showing projected recoveries. Success rates climb to 90% when gas exceeds median by 20%, per OKX feeds on Antidrain benchmarks.
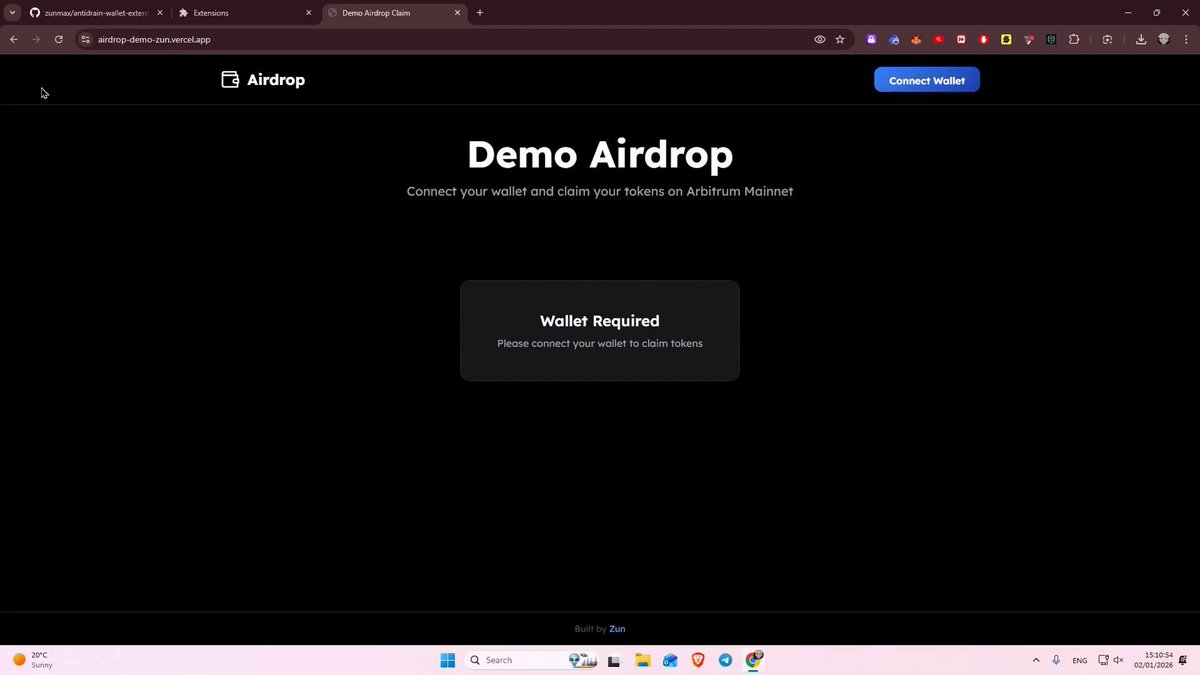
Deploying demands rigor. Host on IPFS for censorship resistance, or Vercel for speed. Audit the contract via OtterSec - I've insisted on this in every migration project. Over 80% malicious delegations mean false positives kill trust; whitelist trusted sponsors like Etherspot from day one.
Outpacing Antidrain: Custom Tool Advantages
Antidrain shines for quick rescues, as Bankless notes, but it's centralized. Your tool decentralizes control, letting users self-custody the recovery contract. Customize for niche threats: add airdrop claimers for morsyxbt-style sweeps, or bridge modules for cross-chain drains. In volatile markets with ETH at $2,237.44, every basis point of recovered value compounds. Custom logic frontruns generic tools by tailoring to specific drainer contracts, boosting sweeper bot bypass EIP-7702 efficacy.
Real-world validation? Simulate via Anvil forks mimicking Pectra chains. Deploy a mock drainer, sign a phishing delegation, then recover. Tools like allthingsweb3. com prove five-minute turnarounds possible; yours can shave to three with optimized bundles. Opinion: Relying on third-parties cedes sovereignty - build once, own forever.
EIP-7702's dual edge: empowerment for builders, peril for the unwary. Revoke fast, or lose it all.
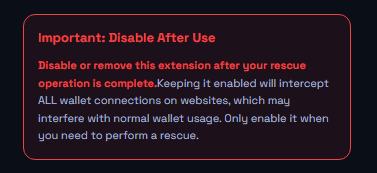
Risks linger, though. Phishing evolves; scammers now mimic recovery UIs. Mitigate with social verification - embed frame checks or domain proofs. Never expose private keys; pure delegation flows suffice. For wallets integrating this, prioritize FRM-grade resilience: multi-sig beneficiaries, timelocks on sweeps. As markets dip 2.48% in 24 hours, drained funds evaporate faster - your tool becomes a lifeline.
Scale it further via 7702migration. com resources. SDKs there streamline compromised EOA rescue, with guides for dApp wrappers. Providers like Alchemy bundle EIP-7702 endpoints; pair with your revocation core for enterprise-grade security. Users reclaim not just tokens, but confidence in Ethereum's abstraction era.
Drainer epidemics peaked post-Pectra, but armed with this blueprint, you frontrun the fray. Deploy, test, recover - risk managed is opportunity regained.







No comments yet. Be the first to share your thoughts!