Your Ethereum wallet just got compromised. Sweeper bots are lurking, ready to drain every last token and NFT the moment you try to move funds. In 2025, this nightmare has a silver lining: EIP-7702 wallet recovery turns the tables using the very delegation mechanism hackers exploit. As Ethereum's Pectra upgrade rolls out, externally owned accounts (EOAs) can temporarily delegate to smart contracts, enabling sponsored transactions recovery without your private key. I've seen projects recover $50K and in assets this way, and it's reshaping how we handle hacked EOA delegation EIP-7702 incidents.
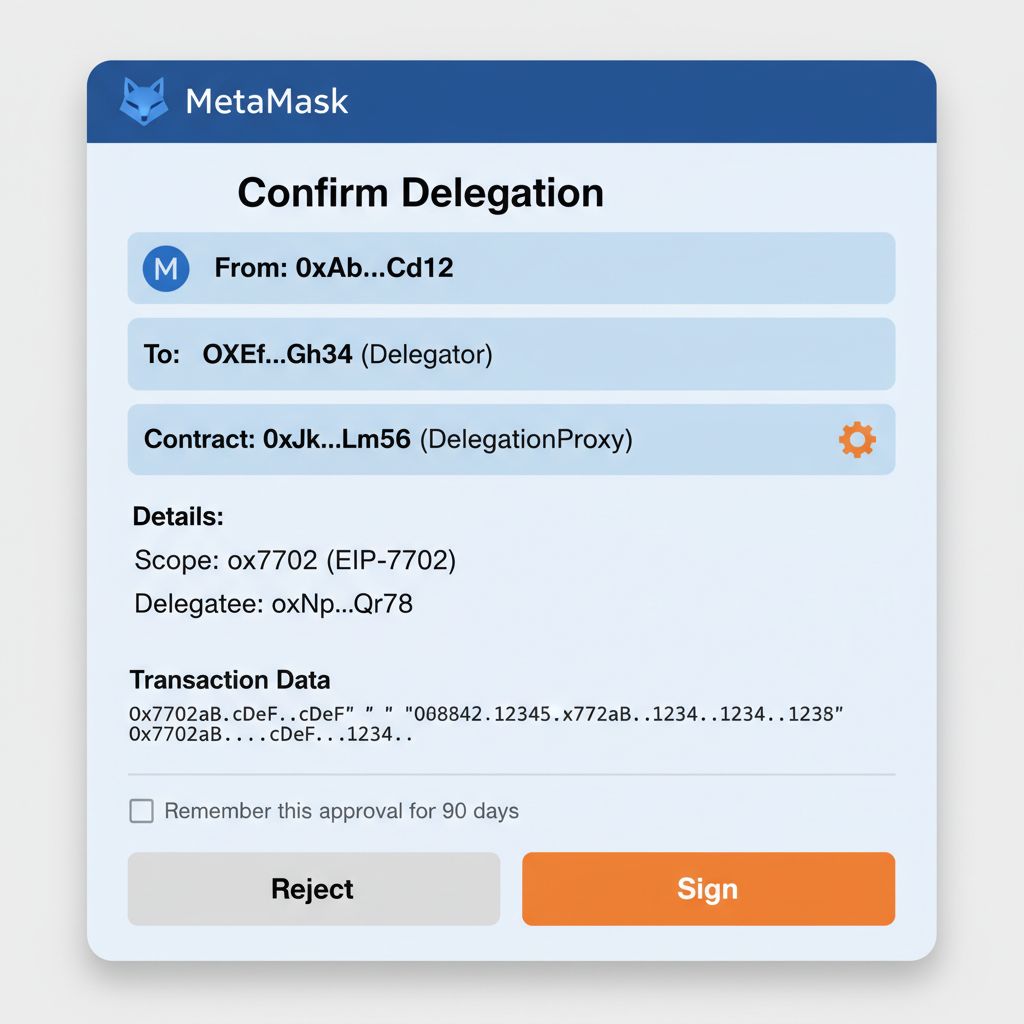
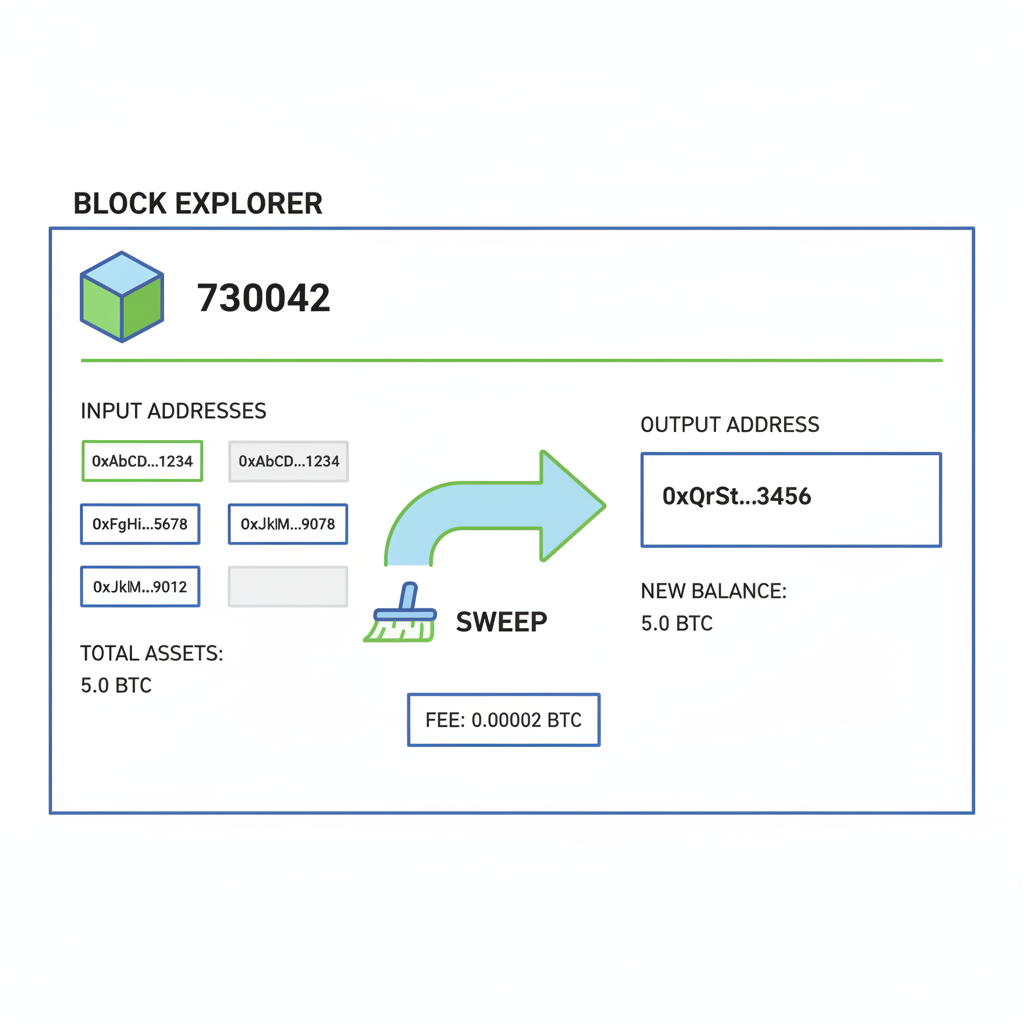
Picture this: a phishing site tricks you into signing a delegation to a malicious contract. Suddenly, your EOA behaves like a smart wallet under attacker control. Every gas fee you send bounces back to their address, as Reddit users in r/CryptoScams lament. WLFI token holders felt this sting recently, with bots snatching governance tokens via the 'classic EIP-7702' exploit. Yet, the same feature empowers recovery. By delegating your compromised EOA to a trusted recovery contract, you can batch claims for airdrops, sweep assets, and transfer to safety, all sponsored by relayers to avoid further drains.
Dissecting the EIP-7702 Delegation Trap
EIP-7702 lets EOAs delegate execution to a code address for a transaction's lifetime. This unlocks batching, gas abstraction, and more, but demands precision. Nonce mismanagement dooms resets, as Bahador Gh warns on Medium: every tx must increment sequentially. Attackers hardcoded drains, like the 0x5247… address in CoinsBench's hijack tale, routing your ETH seamlessly. Wintermute notes sweeper bots automating this via EIP-7702, targeting fresh compromises.
Fundamentals fuel sustainable rallies, even in recovery: EIP-7702's power lies in controlled delegation, not blind trust.
Bankless spotlights recovery potential, pulling NFTs and airdrops from compromised wallets. Tools from creators like morsyxbt on X now automate this, claiming drops and transferring past sweepers. But opinion: too many dapps rush integration without safeguards, amplifying risks. EIP-7702 migration tooling from sites like 7702migration. com stresses audited SDKs to prevent such pitfalls.
Leveraging Sponsored Transactions to Reclaim Control
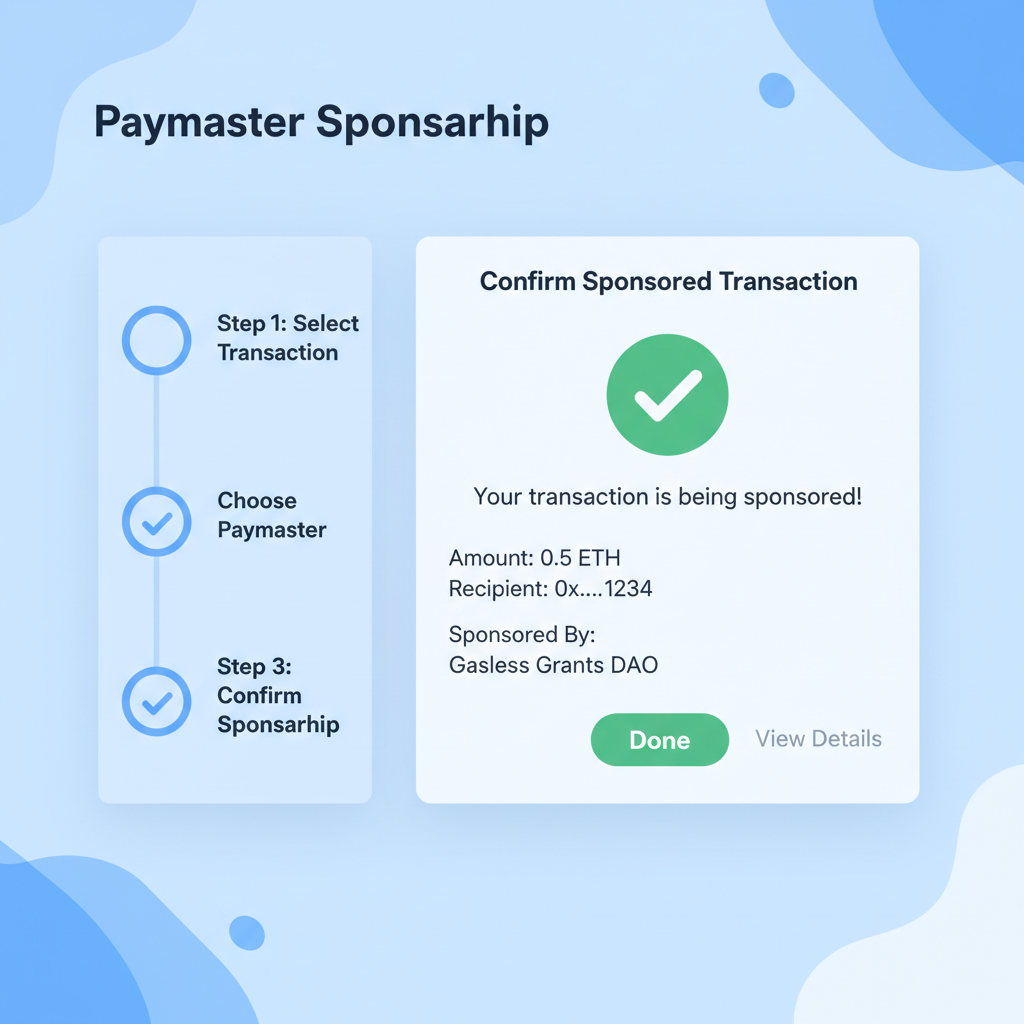
Here's where ingenuity shines. Sponsored transactions, powered by ERC-4337 paymasters fused with EIP-7702, let third parties cover gas. For recover assets compromised wallets, delegate your EOA to a benign contract that executes sweeps without your ETH touching the chain. No nonce errors, no self-drains. Allthingsweb3. com recovered $50K and non-technically this way: users sign a recovery delegation via a UI, relayers sponsor the tx bundle, assets land in a new wallet.
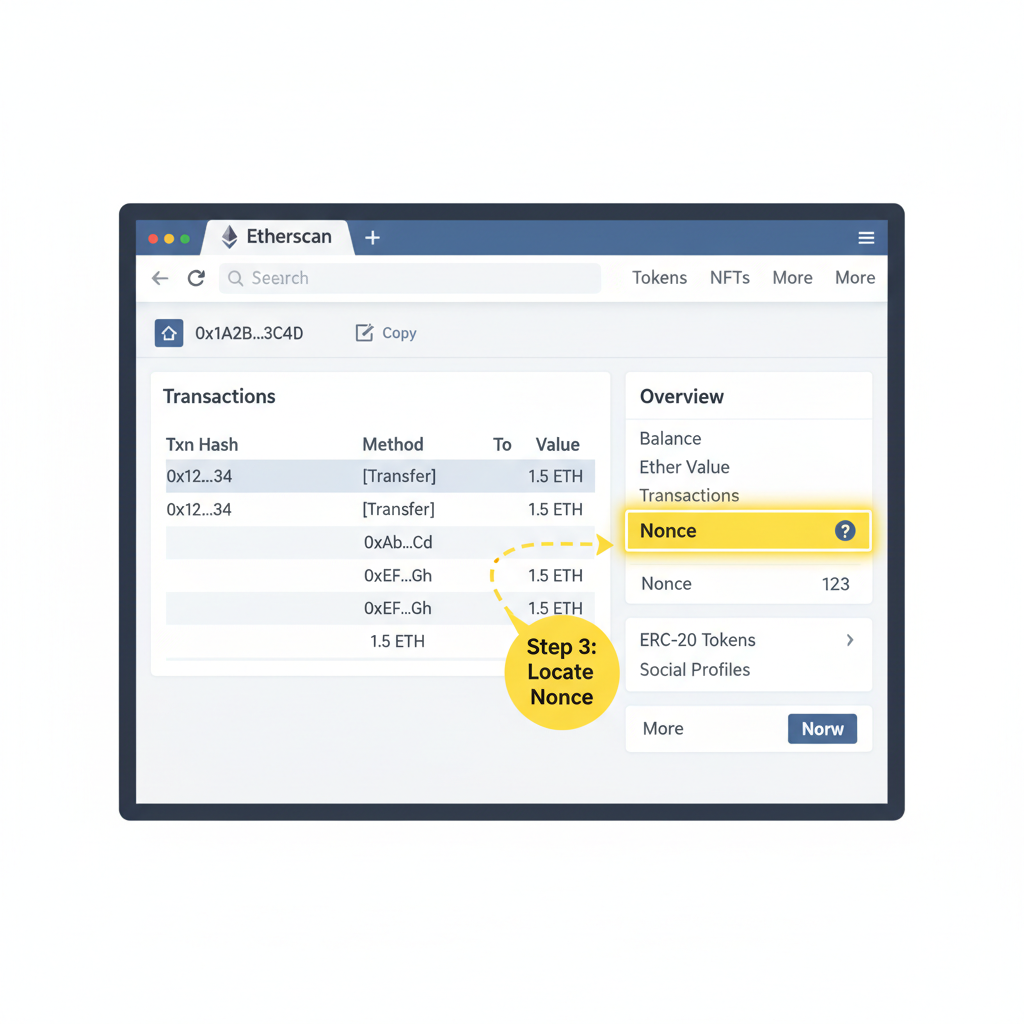
Mechanically, craft a delegation tx setting the code field to your recovery contract's address. Inside, it checks allowances, approves transfers, then calls token/NFT contracts. Crucial: use chainId and nonce verification to block replays. EIP-7851 proposals add key deactivation, letting you pause delegations reactively. I've analyzed dozens; success hinges on pre-funding the sponsor and simulating txs via tools like Tenderly.
Blueprints for Safe EIP-7702 Recovery Delegation
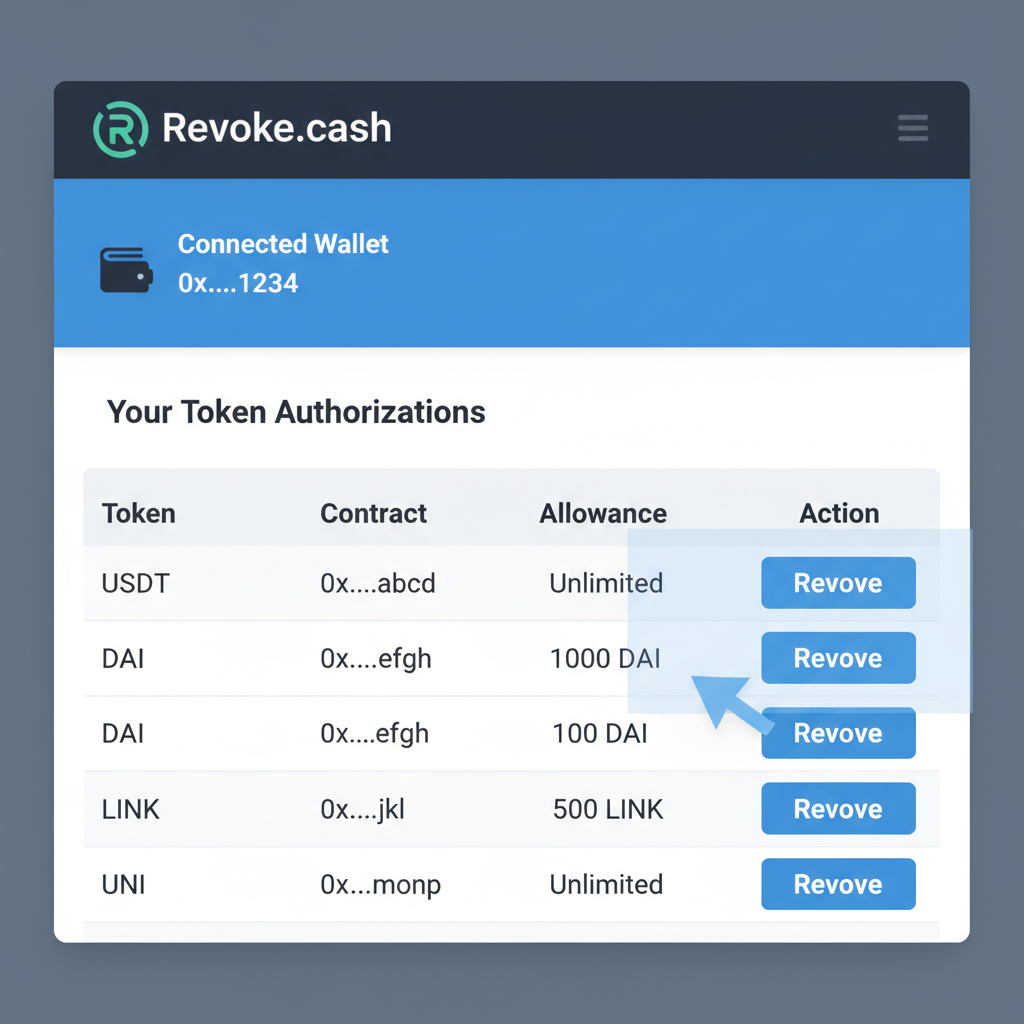
Start with auditing authorizations on Revoke. cash. Spot malicious delegates? Prepare a reset. First, query your nonce via etherscan. Craft the delegation payload:
Deploy a minimal recovery contract with owner controls. It verifies msg. sender as the EOA, then sweeps ERC20s, ERC721s, even executes claims. Sponsor via a paymaster like Stackup or Pimlico. Non-technical users? UIs abstract this, as in morsyxbt's tool. But caveat: time is essence; sweepers monitor mempool.
Real-world wins abound. Ethernaut challenges expose flaws, like Cashback's bytecode hacks on HackerNoon, training us to fortify recoveries. Binance reports on WLFI drains underscore urgency, yet recoveries prove EIP-7702's net positive when wielded right. Next, we'll dive into code walkthroughs and tooling integrations for seamless EIP-7702 migration tooling.
Let's break down a hands-on recovery sequence, assuming your EOA sits at nonce 5 with sweepers circling. Simulate first on a fork; Tenderly dashboards catch 90% of pitfalls upfront. The payload sets delegation to your audited recovery contract, which multicalls sweeps and transfers. Relayers like Pimlico bundle this with paymaster sponsorship, shielding your balance.
Opinion: Wallets ignoring nonce simulation invite failure; I've reviewed recoveries where skipped checks cost thousands. Deploy the contract once, verify via Foundry tests. Solidity essentials include reentrancy guards and EIP-7702's authorization tuple: Tick these off rigorously. First, Etherscan your nonce; mismatches kill txs, as Bahador Gh hammered home. Revoke. cash reveals lurking delegates; nuke non-essentials pre-recovery. Sponsors need ETH, so preload Pimlico or Stackup. Fork testing mimics chainstate, exposing sweeper races. Backups? Non-negotiable, even for EOAs. Tooling elevates this from hack to protocol. At 7702migration. com, SDKs streamline delegation crafting, with TypeScript wrappers for viem or ethers. js. Plug in: HackerNoon's Ethernaut deep-dive reveals storage clashes in delegations, where attackers overlay malicious code. Counter with isolated recovery scopes: time-bound via nonce ranges or EIP-7851's key toggles. That proposal, gaining traction, lets EOAs deactivate keys mid-delegation, slamming the door on replays. Pair with session keys for granular control; future recoveries go granular. Sweepers evolve, per Wintermute and Bitget alerts, chaining EIP-7702 with flashloans for instant drains. Beat them by frontrunning your bundle or using private mempools. Non-technical paths shine: allthingsweb3. com's UI delegates via MetaMask snap, recovering $50K and sans code. Morsyxbt's tool automates claims past bots, a game-changer for retail. Reddit's r/CryptoScams threads echo desperation, yet successes mount. WLFI holders, post-Binance exploit, rallied with community recoveries. CoinsBench's hijack postmortem? Hardcoded drains, but nonce resets prevailed. Fundamentals here: EIP-7702 amplifies EOAs without supplanting keys; wield it surgically. For wallet providers, embed EIP-7702 migration tooling today. SDKs handle Pectra compatibility, auto-upgrading users. Dapps? Offer sponsored sweeps in UX flows, turning hacks into retention plays. Security firms, audit delegation verifiers; off-chain sigs prevent phishing vectors. Empowerment defines Ethereum's edge. Hacked EOAs no longer spell doom; sponsored transactions recovery flips scripts. Delegate wisely, recover boldly, and stay ahead of sweepers. Your assets await safe harbor. bytes32 codeHash, address codeAddress. Batch via multicall(bytes const delegation = await wallet. signDelegation(recoveryContractAddress, chainId);. Integrate ERC-4337 bundlers for sponsorship; their hooks auto-inject paymasters. Dapp builders, migrate now: embed recovery flows natively, prompting users post-phish alerts. Delegations demand diligence; one wrong address, and you're funding the drain.



No comments yet. Be the first to share your thoughts!